Table of Contents
- Exploring Booter Services
- IP Spoofing and Layer 4 Attacks
- IP Grabbers and Their Usage
- Advanced Booter Panels
- Amplification Methods in Stresser Services
Exploring Booter Services

Through strategic load testing, booter tools expose vulnerabilities and system weaknesses.
They reveal weak points in server infrastructure, helping organizations preemptively reinforce their cybersecurity defenses.
IP Spoofing and Layer 4 Attacks
IP spoofing techniques in network-based intrusions can
conceal attack origins, making it harder to trace attackers.
Spoofing provides an added layer of anonymity, which is critical in maintaining stealth during network tests.
IP Grabbers and Their Usage

IP grabbers provide actionable insights for network management,
helping organizations detect suspicious traffic and protect sensitive data.
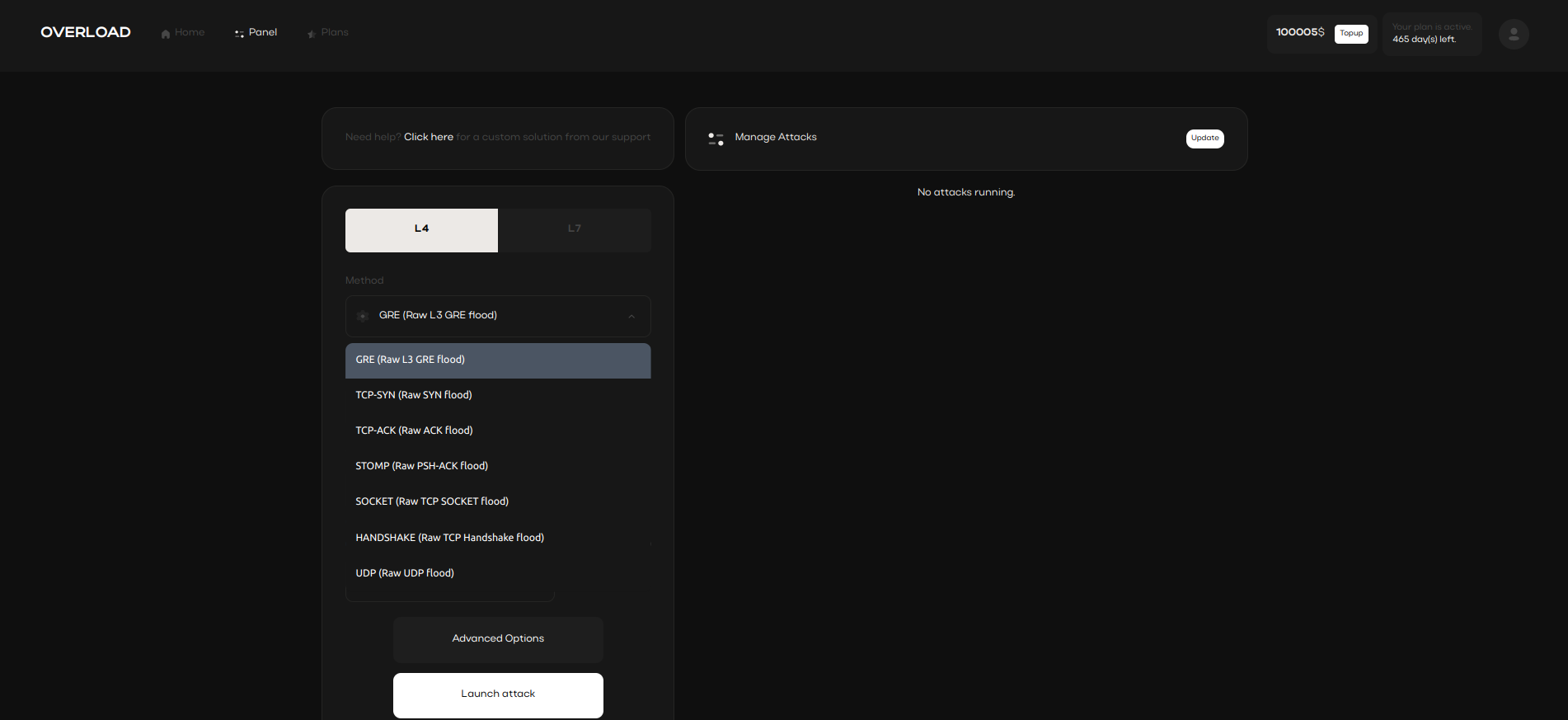
Advanced Booter Panels

Booter tools provide seamless access to network testing,
offering user-friendly controls and comprehensive analysis reports.
Amplification Methods in Stresser Services

CLDAP, DNS, and NTP techniques amplify network requests, generating an overload
that tests system capacity limits. These methods increase traffic impact significantly, often resulting in substantial strain on systems.
- DNS reflection method
- NTP boost method
- CLDAP traffic magnification